WHMCS Killer v4 Coded in Latest php version Tools Server R00t Domain Resellers Clients R00ts Clients Hosting Accounts Clients CC Clients Password NEw DEsign
WSO SHELL 2023
[Hacker Tools] cPanel/WHM/WebMail Cracker - Create RDP - Getting Passwords - Finder .accesshash/WHM - Finder .my.cnf/cPanel - Auto Change Admin User WordPress/Joomla/OpenCart - Zone-h Poster - Install BackDoor [Spammer Tools] Create SMTP - Create Mailer - Mail Sending Checker - Redirects - Getting Emails-List - Emails-list Filter [Other Features] Adminer - WHMCS Killer v4 - Unzip - Config Grabber[Advanced] - Server Jumping - Cgi Shell - Back Connect - Domains List [Supported] php 5.x - php 7.x - php 8.x Password:dadsec
: Social engineering attacks that use fraudulent emails or websites to steal user data (login credentials, credit card numbers).
The goal of information security is not to eliminate risk entirely—which is impossible—but to manage it to an acceptable level. By balancing the and staying vigilant against new threats, individuals and organizations can protect their most valuable asset: information. The Basics of Information Security: Understandi...
Examples : Encryption, multi-factor authentication (MFA), and access control lists. : Social engineering attacks that use fraudulent emails
The foundation of any information security program is the . These three principles serve as the industry standard for evaluating security posture. multi-factor authentication (MFA)
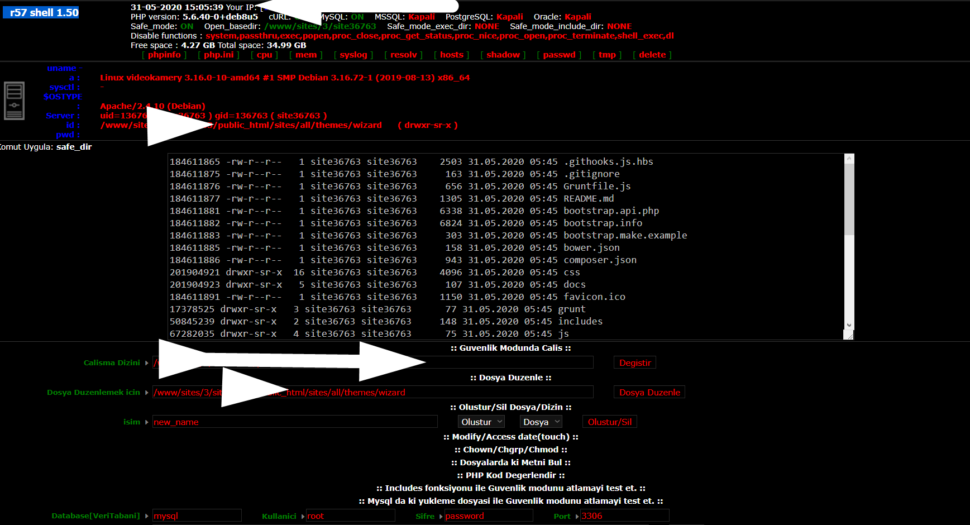
Wr57 shell txt
visit the most interesting R57 pages, well-liked by users from your country and all over the world, or check the rest of r57.biz data below. R57.biz is a website, reported to be malware-infected or hijacked, so you should stay away from it until the problem is resolved. We found that English is the preferred language on R57 pages. Their most used social media is Facebook with about 93% of all user votes and reposts.
: Social engineering attacks that use fraudulent emails or websites to steal user data (login credentials, credit card numbers).
The goal of information security is not to eliminate risk entirely—which is impossible—but to manage it to an acceptable level. By balancing the and staying vigilant against new threats, individuals and organizations can protect their most valuable asset: information.
Examples : Encryption, multi-factor authentication (MFA), and access control lists.
The foundation of any information security program is the . These three principles serve as the industry standard for evaluating security posture.